User authentication is an integral part of our lives; we authenticate ourselves to personal computers and a variety of other things several times a day. Authentication is burdensome. When we wish to access to a computer or a resource, it is an additional task that we need to perform -- an interruption in our workflow. In this dissertation, we study people’s authentication behavior and attempt to make authentication to desktops and smartphones less burdensome for users.
First, we present the findings of a user study we conducted to understand people’s authentication behavior: things they authenticate to, how and when they authenticate, authentication errors they encounter and why, and their opinions about authentication. In our study, participants performed about 39 authentications per day on average; the majority of these authentications were to personal computers (desktop, laptop, smartphone, tablet) and with passwords, but the number of authentications to other things (e.g., car, door) was not insignificant. We saw a high failure rate for desktop and laptop authentication among our participants, affirming the need for a more usable authentication method. Overall, we found that authentication was a noticeable part of all our participants’ lives and burdensome for many participants, but they accepted it as cost of security, devising their own ways to cope with it.
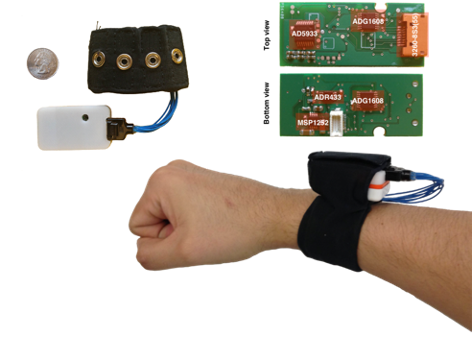
Second, we propose a new approach to authentication, called bilateral authentication, that leverages wrist-wearable technology to enable seamless authentication for things that people use with their hands, while wearing a smart wristband. In bilateral authentication two entities (e.g., user’s wristband and the user’s phone) share their knowledge (e.g., about user’s interaction with the phone) to verify the user’s identity. Using this approach, we developed a seamless authentication method for desktops and smartphones. Our authentication method offers quick and effortless authentication, continuous user verification while the desktop (or smartphone) is in use, and automatic deauthentication after use. We evaluated our authentication method through four in-lab user studies, evaluating the method’s usability and security from the system and the user’s perspective. Based on the evaluation, our authentication method shows promise for reducing users’ authentication burden for desktops and smartphones.
 Biometric identification/verification.
In this work we address two critical challenges. First, we evaluate
the use of bioimpedance for recognizing who is wearing
wireless sensors and show that bioimpedance is a feasible
biometric. Second, we investigate the use of accelerometers for
verifying whether two of these wireless sensors are on the same
person and show that our method is successful as distinguishing
between sensors on the same body and on different bodies. We stress
that any solution to these problems must be usable, meaning the user
should not have to do anything but attach the sensor to their body
and have them just work. This work is best described in Cornelius'
PhD thesis
[cornelius:thesis],
and also appeared in several papers
[cornelius:wearable,
cornelius:impedance,
cornelius:j-same-body,
cornelius:same-body,
cornelius:biometrics-poster].
We also conducted an early investigation into the prospect of
identifying people with their 'vocal resonance', that is, the sound of
their voice as recorded through their body
[cornelius:voice-tr];
this work later was finished under the
THaW project.
Biometric identification/verification.
In this work we address two critical challenges. First, we evaluate
the use of bioimpedance for recognizing who is wearing
wireless sensors and show that bioimpedance is a feasible
biometric. Second, we investigate the use of accelerometers for
verifying whether two of these wireless sensors are on the same
person and show that our method is successful as distinguishing
between sensors on the same body and on different bodies. We stress
that any solution to these problems must be usable, meaning the user
should not have to do anything but attach the sensor to their body
and have them just work. This work is best described in Cornelius'
PhD thesis
[cornelius:thesis],
and also appeared in several papers
[cornelius:wearable,
cornelius:impedance,
cornelius:j-same-body,
cornelius:same-body,
cornelius:biometrics-poster].
We also conducted an early investigation into the prospect of
identifying people with their 'vocal resonance', that is, the sound of
their voice as recorded through their body
[cornelius:voice-tr];
this work later was finished under the
THaW project.
